Cloud Storage Credentials Guide
This guide will help you obtain the necessary credentials to use Captain with your cloud storage provider.
AWS S3 Credentials
To index files from Amazon S3 buckets, you’ll need an AWS Access Key ID and Secret Access Key.
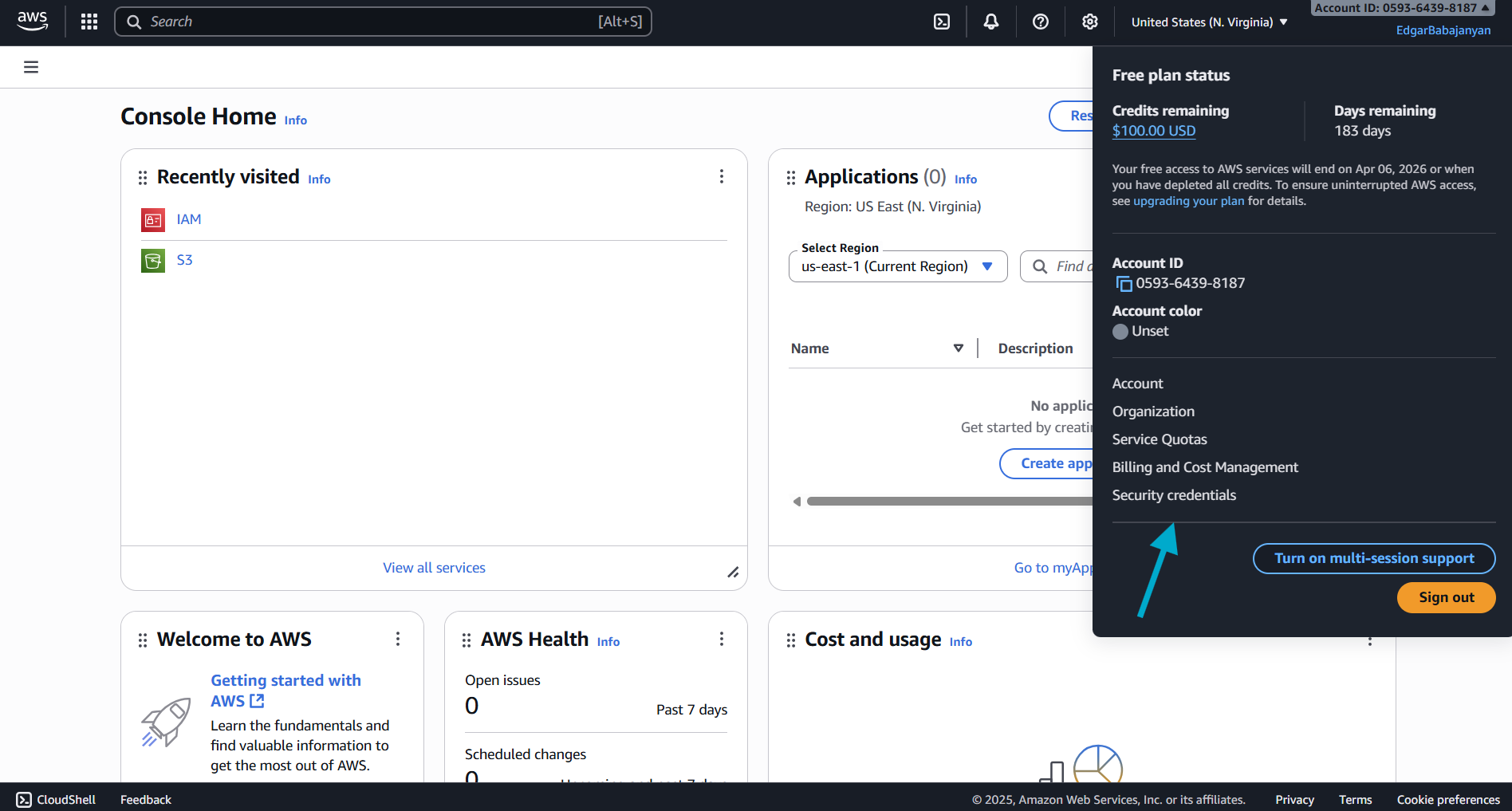
Step 1: Navigate to IAM Security Credentials
- Log in to the AWS Console
- Click on your account name in the top-right corner
- Select Security credentials from the dropdown menu
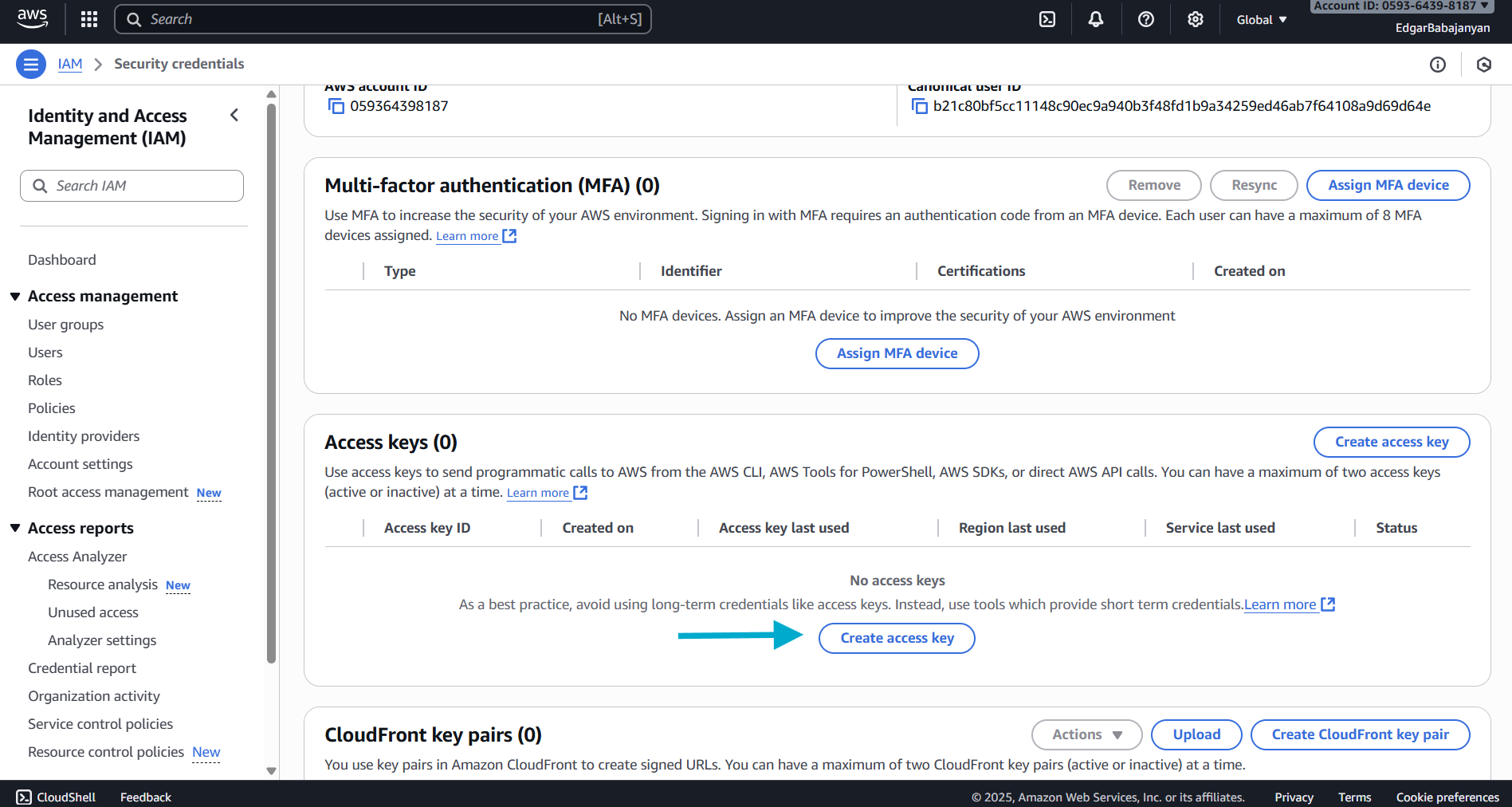
Step 2: Create Access Key
- Scroll down to the Access keys section
- Click the Create access key button
Step 3: Retrieve Your Credentials
- Your Access Key ID and Secret Access Key will be displayed
- Important: This is the only time you can view the Secret Access Key
- Click Show to reveal the Secret Access Key
- Copy both the Access Key ID and Secret Access Key to a secure location
- Optionally, download the
.csvfile for safekeeping
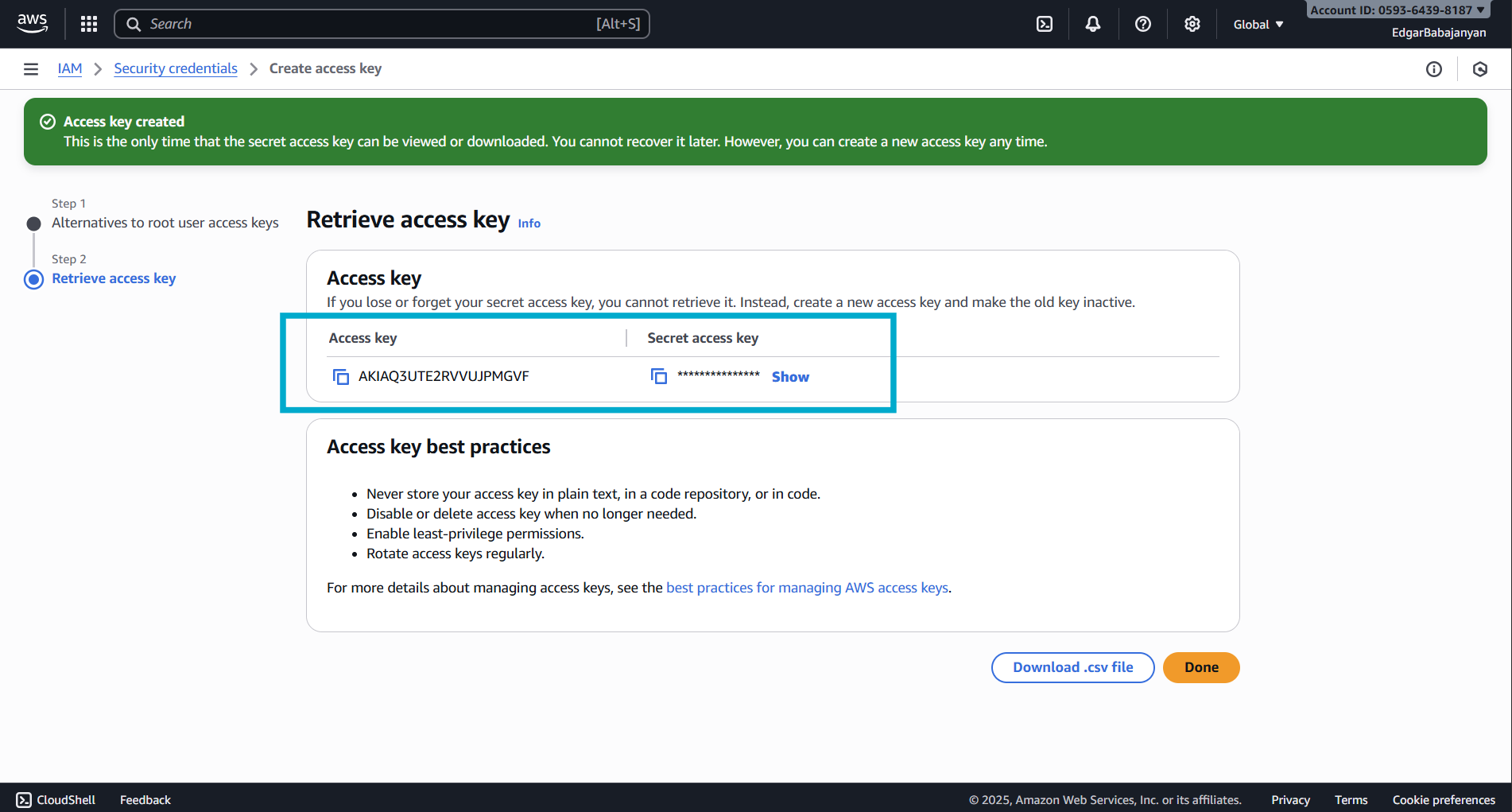
Best Practices for AWS Access Keys
- Never store your access key in plain text, in a code repository, or in code
- Disable or delete access keys when no longer needed
- Enable least-privilege permissions
- Rotate access keys regularly
Required IAM Permissions
Your AWS access key needs the following permissions to work with Captain:
For read-only access to S3 buckets:
Replace your-bucket-name with your actual S3 bucket name.
Google Cloud Storage Credentials
To index files from Google Cloud Storage buckets, you’ll need a Service Account JSON key.
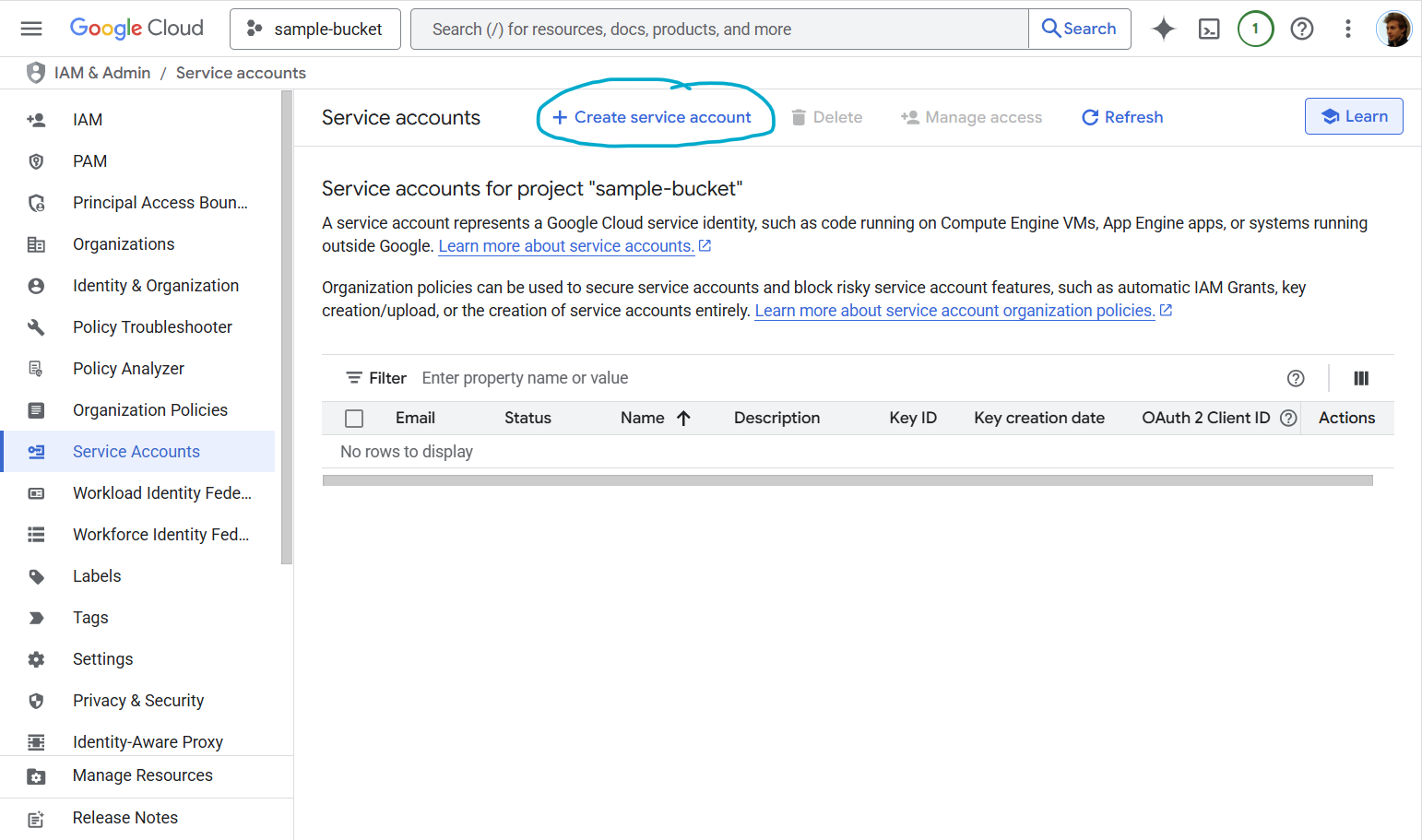
Step 1: Navigate to Service Accounts
- Go to Google Cloud Console
- Navigate to IAM & Admin → Service Accounts
- Click Create Service Account
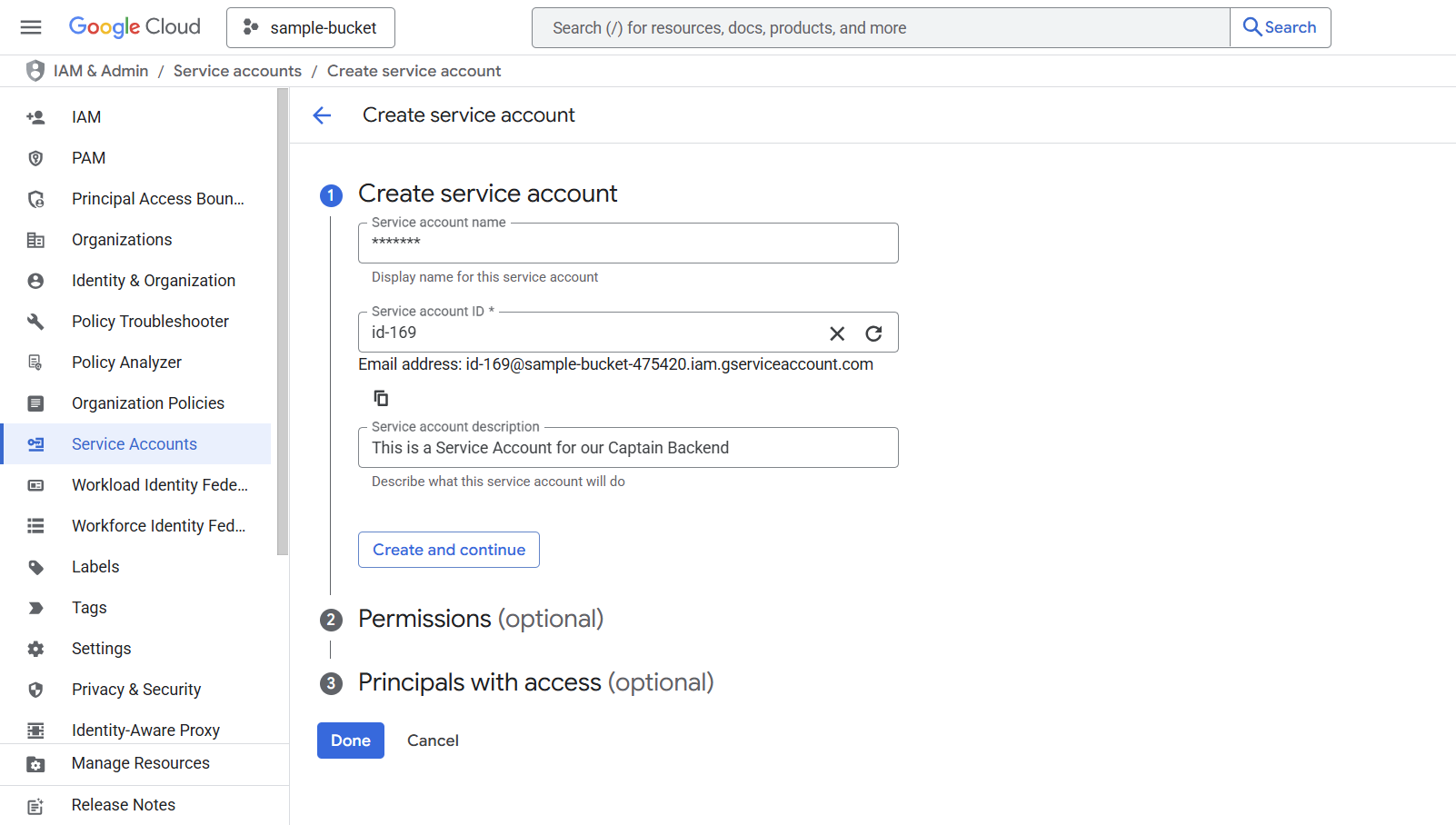
Step 2: Create Service Account
- Enter a Service account name (e.g.,
captain-storage-access) - Add a Service account description (optional but recommended)
- The Service account ID will be auto-generated
- Click Create and continue
Step 3: Grant Permissions
Under Grant this service account access to project, choose the appropriate role based on your needs:
For read-only access to buckets/objects:
- Role: Storage Object Viewer (
roles/storage.objectViewer)
For read/write access:
- Role: Storage Object Admin (
roles/storage.objectAdmin)
For full bucket management:
- Role: Storage Admin (
roles/storage.admin)
Click Continue → Done
Step 4: Create and Download JSON Key
- You’ll now see your new service account in the list
- Click on the service account name
- Navigate to the Keys tab
- Click Add Key → Create New Key
- Select JSON as the key type
- Click Create
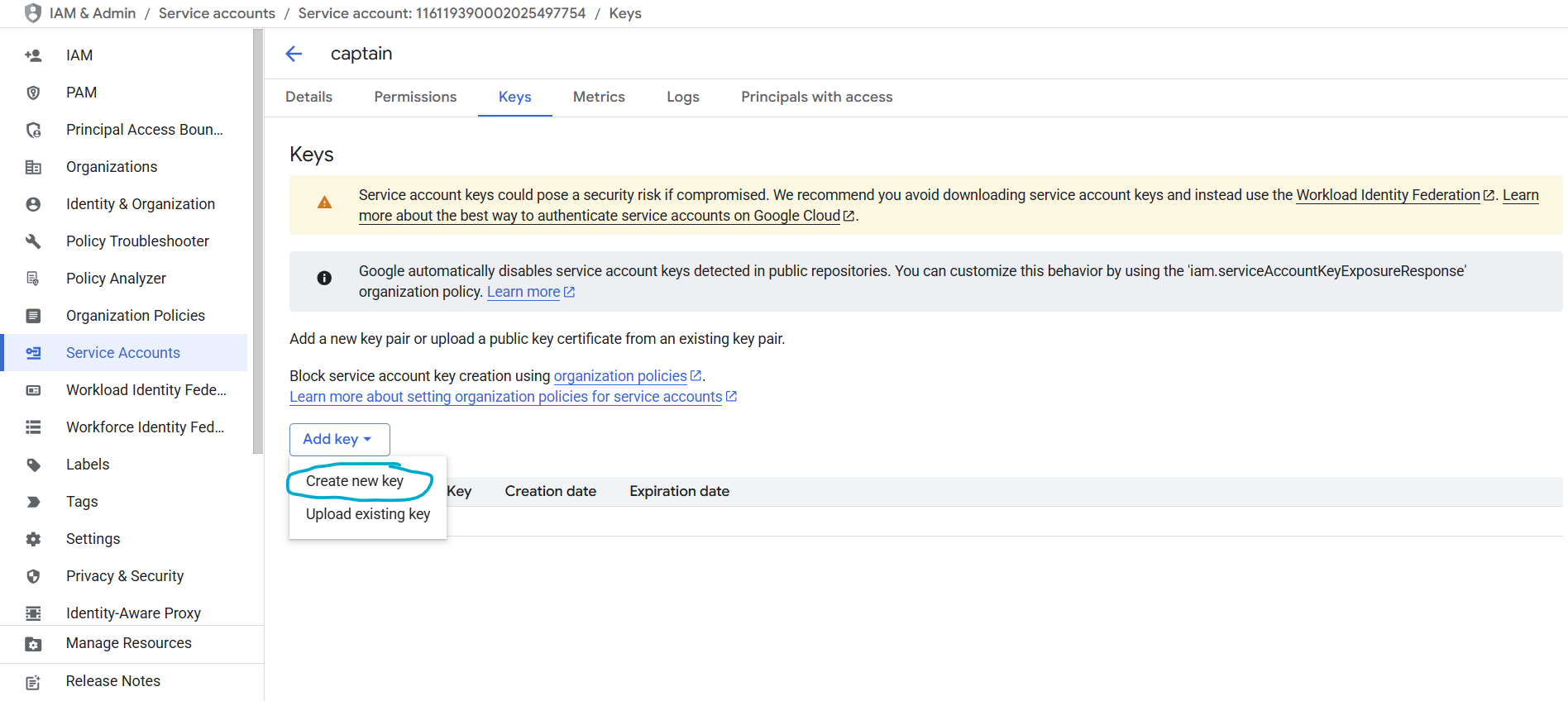
The JSON key file will automatically download to your computer. This file contains your service account credentials.
JSON Key File Format
Your downloaded JSON key will look like this:
Using the Service Account with Captain
When using Captain with Google Cloud Storage, you’ll typically need to:
- Store the JSON key file securely on your server
- Set the
GOOGLE_APPLICATION_CREDENTIALSenvironment variable to point to the JSON file path:
Or load it programmatically in your application.
Best Practices for Service Account Keys
- Service account keys could pose a security risk if compromised
- Never commit service account keys to version control
- Store keys securely using secret management services
- Rotate keys regularly
- Delete unused service accounts and keys
- Consider using Workload Identity Federation for more secure authentication (advanced)
- Google automatically disables service account keys detected in public repositories
Using Credentials with Captain
Once you have your credentials, you can use them with Captain’s indexing endpoints:
AWS S3 Example
Google Cloud Storage Example
Security Reminders
- Never share your credentials in public forums, chat messages, or email
- Never commit credentials to version control systems (Git, SVN, etc.)
- Use environment variables or secure secret management services in production
- Rotate credentials regularly to minimize security risks
- Apply least-privilege permissions - only grant the minimum access needed
- Monitor credential usage through AWS CloudTrail or Google Cloud Audit Logs
Troubleshooting
AWS Issues
Error: “Invalid AWS credentials”
- Verify your Access Key ID and Secret Access Key are correct
- Check that the access key is active in the IAM console
- Ensure your IAM user/role has the necessary S3 permissions
Error: “Access Denied”
- Verify your IAM permissions include
s3:GetObjectands3:ListBucket - Check bucket policies and ensure they allow your IAM user/role
- Verify the bucket region matches the
bucket_regionparameter
Google Cloud Issues
Error: “Invalid service account credentials”
- Verify the JSON key file is valid and not corrupted
- Check that the service account is enabled
- Ensure the service account has the necessary Storage permissions
Error: “Permission denied”
- Verify the service account has the appropriate Storage role
- Check that the bucket exists and the service account has access
- Review IAM permissions in the Google Cloud Console
Need Help?
If you encounter issues obtaining or using your cloud storage credentials, contact Captain support:
- Email: support@runcaptain.com
- Phone: +1 (260) CAP-TAIN